Cryptography is a funny thing. Supposedly, if you do the right kind of maths to a message, you can send it off to somebody else, and as long as they’re the only one that knows a secret little thing, nobody else will be able to read it. We have all sorts of apps for this, too, that are specifically built for privately messaging other people.
Only… sometimes just having such an app is enough to get you in trouble. Even just the garbled message itself could be proof against you, even if your adversary can’t read it. Enter The Guardian. The UK-based media outlet has deployed a rather creative and secure way of accepting private tips and information, one which seeks to provide heavy cover for those writing in with the hottest scoops.
Hiding In Plain Sight
There are plenty of encrypted messaging apps out there, of greater or lesser value. Ultimately, though, they all have a similar flaw. If you have one of these ultra-secure apps on your phone, or malicious authorities capture you sending lots of messages to such a server, it can be somewhat obvious that you’re doing something worth hiding. You might not be—you might just have a penchant for keeping your fantasy football submissions under wraps. Regardless, using heavily-encrypted messaging systems can put a bit of a beacon on you, at a time when you might be hoping to stay as unobtrusive as possible.
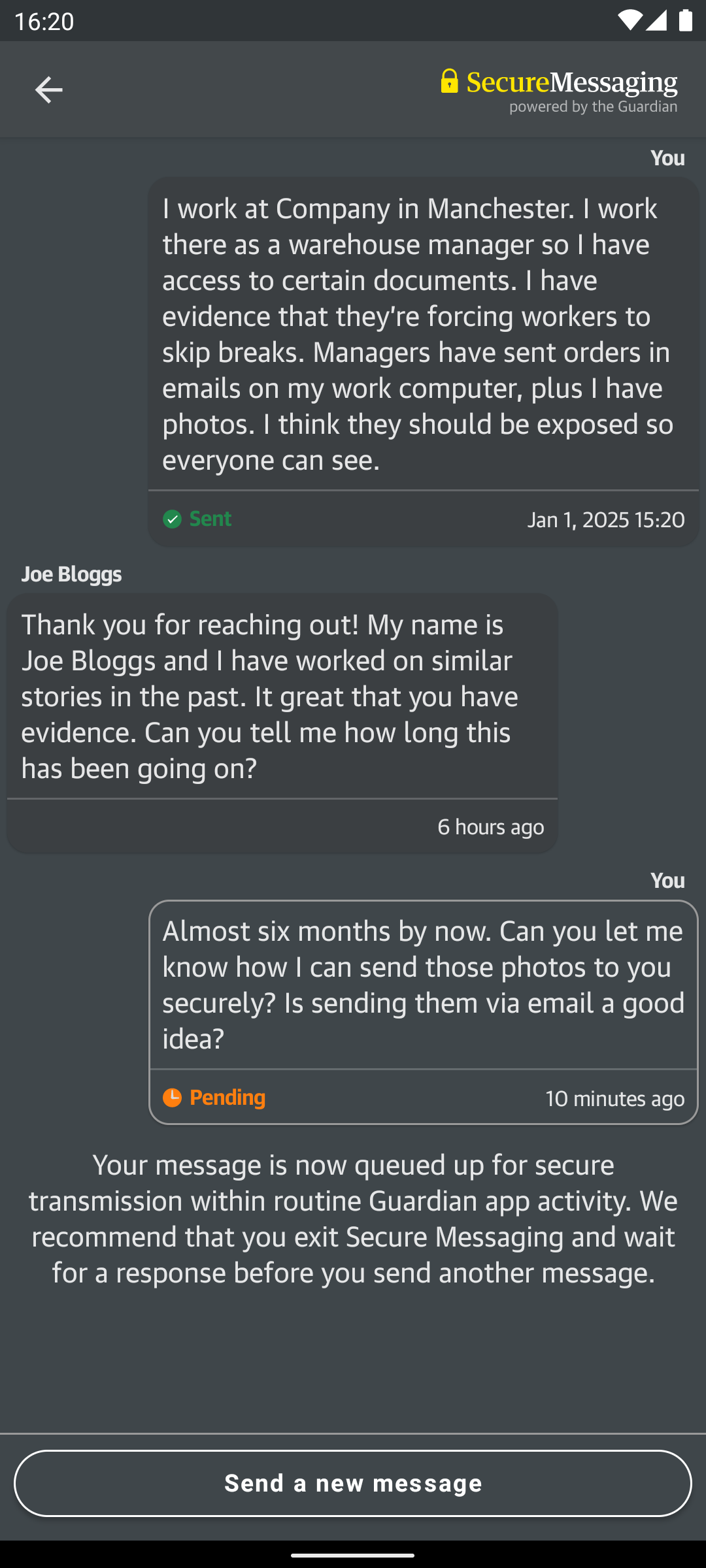
It’s this precise problem that The Guardian and developers at the University of Cambridge hoped to solve with the CoverDrop messaging system. It’s designed specifically for users of news apps to be able to make confidential submissions to journalists without leaving a telltale trail of evidence that could reveal their actions. It’s intended to be suitable for implementation by a wide range of news agencies if so desired, as laid out in the project white paper.
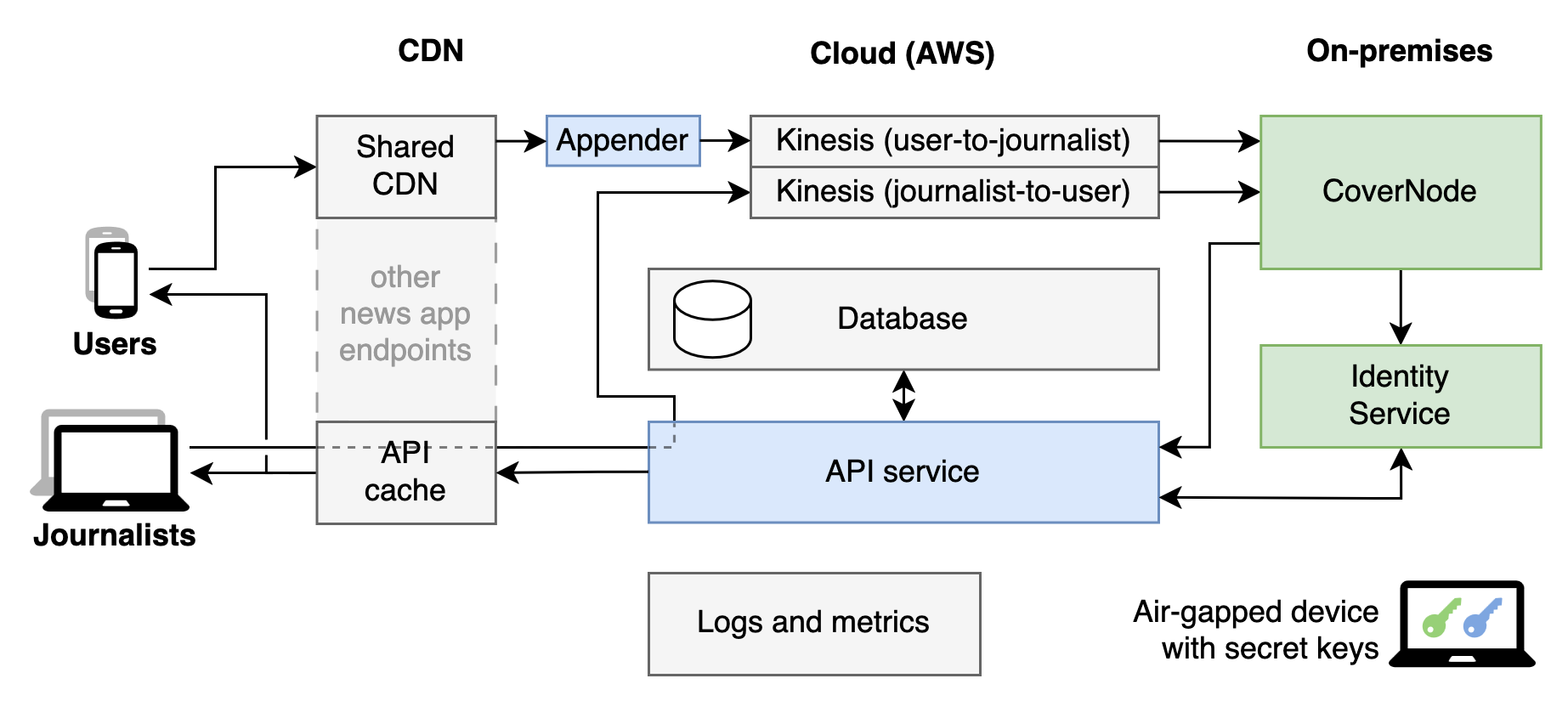
The CoverDrop system uses multiple techniques to not just encrypt messages, but hide whether or not any messaging is happening in the first place. The key is that CoverDrop is integrated into every copy of the Guardian’s news app out there, and each app sends small amounts of encrypted information to the system at regular intervals. Most of the time, this is just meaningless text with no information content whatsoever.
That is, unless somebody has a message to send to a journalist. In that case, the message and the source’s public key is encrypted with the journalist’s public key, packaged up, and sent in such a way that it appears fundamentally no different to any other garbage message that is being sent to the CoverDrop servers. Both real and cover messages are encrypted the same way and have the same length, and are sent at the same times, so anyone monitoring network traffic won’t be able to tell the difference.
At the receiving end, CoverDrop’s secure servers remove an initial layer of encryption to filter out real messages from the cover messages. These are then provided to journalists via a dead drop delivery system, which pads the still-encrypted real messages with some cover messages to ensure the drops are always the same size. In the event a dead drop contains a message for a given journalist, they can decrypt it since it was encrypted with their public key in the first place. Since the messages also include the source’s public key, replies can be sent in the reverse fashion in a similarly secure way.
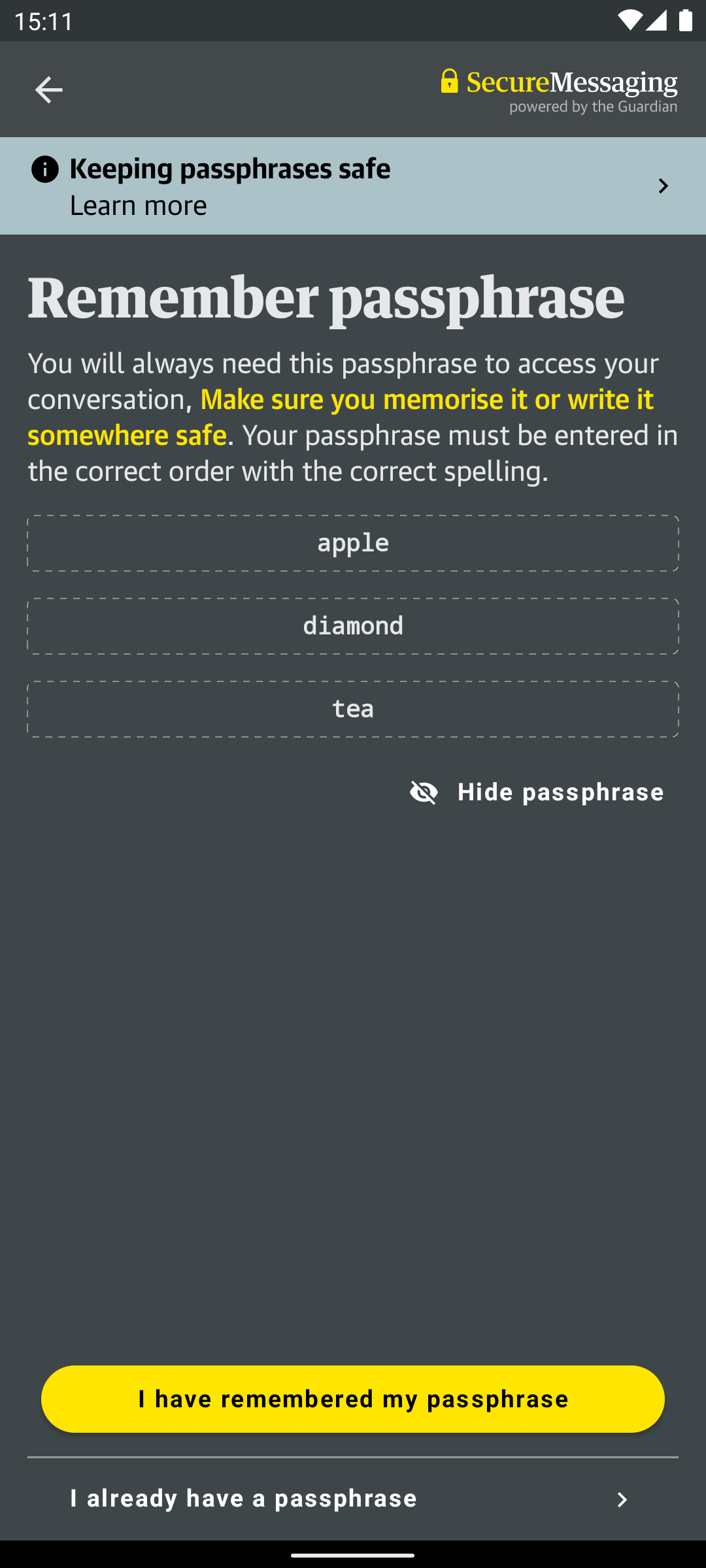
As for on-device security, the system is designed to be as unrevealing as possible as to whether it has been used for secure messaging or not. Message storage vaults used by the app are encrypted, maintained at a regular size, and are routinely modified at regular periods whether covert messages are being sent or not. Unless the decryption passphrase is known, there is no obvious evidence that the app has been used to send any messages at all.
For those eager to implement the system, or merely audit its functionality, the CoverDrop codebase is available on Github. Providing a secure and deniable method of submitting sensitive tips is desirable to many newsrooms, which could lead to wider adoption or similar systems popping up elsewhere. Of course, no system is absolutely secure, but having a messaging system that focuses on more than just simple encryption will be a boon to those looking to communicate with less fear of surveillance or retribution.