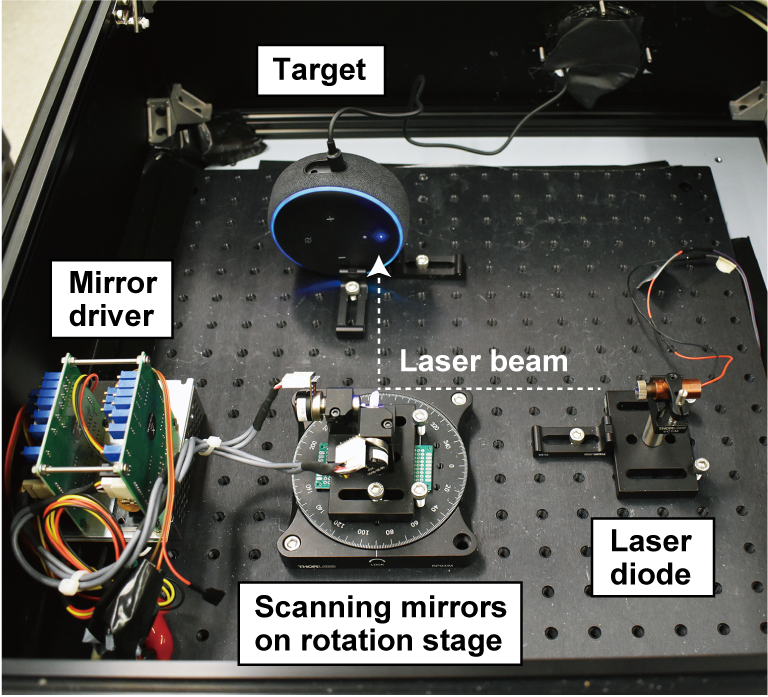
 In one of the cooler hacks we’ve seen recently, a bunch of hacking academics at the University of Michigan researched the ability to flicker a laser at audible sound frequencies to see if they could remotely operate microphones simply by shining a light on them. The results are outstanding.
In one of the cooler hacks we’ve seen recently, a bunch of hacking academics at the University of Michigan researched the ability to flicker a laser at audible sound frequencies to see if they could remotely operate microphones simply by shining a light on them. The results are outstanding.
While most Hackers will have heard about ‘The Thing’ – a famous hack where Russian KGB agents would aim a radio transmitter at the great seal in the US embassy, almost none of us will have thought of using lasers shined in from distant locations to hack modern audio devices such as Alexa or Google Assistant. In the name of due diligence, we checked it out on Wikipedia: ‘The Photoacoustic Effect’ , and indeed it is real – first discovered in 1880 by Alexander Bell! The pulsing light is heating the microphone element and causing it to vibrate along with the beam’s intensity. Getting long range out of such a system is a non-trivial product of telescopes, lasers, and careful alignment, but it can be made to work.
Digging deeper into the hack, we find that the actual microphone that is vulnerable is the MEMS type, such as the 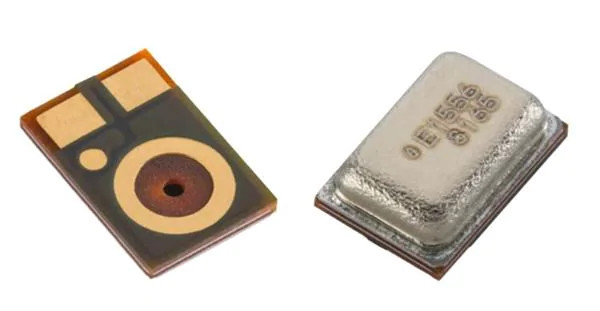 Knowles SPV0842LR5H. This attack is relatively easy to prevent; manufacturers would simply need to install screens to prevent light from hitting the microphones. For devices already installed in our homes, we recommend either putting a cardboard box over them or moving them away from windows where unscrupulous neighbors or KGB agents could gain access. This does make us wonder if MEMS mics are also vulnerable to radio waves.
Knowles SPV0842LR5H. This attack is relatively easy to prevent; manufacturers would simply need to install screens to prevent light from hitting the microphones. For devices already installed in our homes, we recommend either putting a cardboard box over them or moving them away from windows where unscrupulous neighbors or KGB agents could gain access. This does make us wonder if MEMS mics are also vulnerable to radio waves.
As far as mobile phones are concerned, the researchers were able to talk into an iPhone XR at 10 metres, which means that, very possibly, anybody with a hand held ultra violet / infra red equipped flashlight could hack our phones at close range in a bar, for example. The counter-measures are simple – just stick some black electrical tape over the microphone port at the bottom of the phone. Or stay out of those dodgy bars.